- Category: August 2015 - Security
 Advanced Persistent Threats (APTs) exploit the key weaknesses of today’s common IT infrastructures in order to steal intellectual property and sabotage business-critical production environments, explains Imperva, a leading provider of cyber security solutions. The company is specialized in protecting business critical data and applications—in the cloud and on-premises – and therefore a good source for finding out all about APT.
Advanced Persistent Threats (APTs) exploit the key weaknesses of today’s common IT infrastructures in order to steal intellectual property and sabotage business-critical production environments, explains Imperva, a leading provider of cyber security solutions. The company is specialized in protecting business critical data and applications—in the cloud and on-premises – and therefore a good source for finding out all about APT.
There are hundreds of millions of malware variations, which makes it extremely challenging to protect organizations from APT, and Imperva is specialized in providing a solution for the problem, as we showed already last week.
“APTs infiltrate production environments by compromising users via email and social engineering techniques, or by launching direct attacks against websites or web applications”, the company explains. “In both scenarios, adversaries then steal passwords and drop “backdoors” that will enable them to operate “invisibly” within the organization’s ‘trusted zone’.”
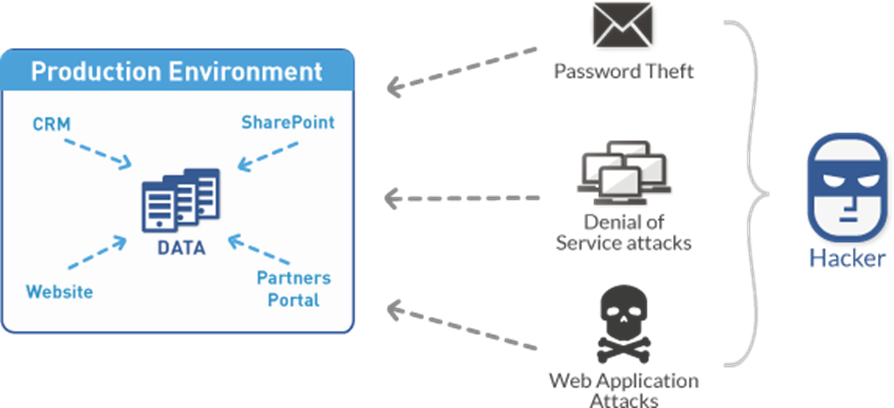
Image: Incapsula
While APT activities are hard to detect, the command and control network traffic associated with APT can be detected at the network layer level. According to experts, deep log analyses and log correlation from various sources can be useful in detecting APT activities. Agents can be used to collect logs (TCP and UDP) directly from assets into a syslog server. Then a Security Information and Event Management (SIEM) tool can correlate and analyze logs.
Then, a good log correlation tool can be used to filter out the legitimate traffic, so security staff can focus on the confounding factors. Fact is that the actors behind APT create a growing and changing risk to organizations' financial assets, intellectual property, and reputation by following a continuous process (as seen in the APT life cycle).

Source: Wikipedia - APT life cycle
APTs use a variety of intelligence gathering techniques to access sensitive information, commonly for the purpose to place malicious codes on one or multiple computers for specific tasks and to remain undetected for the longest possible period.
In 2013, for instance, American cybersecurity firm Mandiant rose to fame when it released a report on alleged Chinese attacks using APT methodology between 2004 and 2013 that followed a similar lifecycle:
• Initial compromise – performed by use of social engineering and spear phishing, over email, using zero-day viruses; or planting malware on a website that the victim employees will be likely to visit.
• Establish foothold – plant remote administration software in victim's network, create network backdoors and tunnels allowing stealth access to its infrastructure.
• Escalate privileges – use exploits and password cracking to acquire administrator privileges over victim's computer and possibly expand it to Windows domain administrator accounts.
• Internal reconnaissance – collect information on surrounding infrastructure, trust relationships, Windows domain structure.
• Move laterally – expand control to other workstations, servers and infrastructure elements and perform data harvesting on them.
• Maintain presence – ensure continued control over access channels and credentials acquired in previous steps.
• Complete mission – extricate data from victim's network.
In incidents analyzed by Mandiant, the average period over which the attackers controlled the victim's network was one year - with the longest at almost five years.
By the way, individual hackers are usually not referred to as an APT, as they rarely have the resources to be both advanced and persistent.
By MediaBUZZ


