 The number of people working from home has risen astronomically this year due to Covid-19. Consequently, numerous companies have been reliant on remote desktop connections to enable their employees to access their work computer from home.
The number of people working from home has risen astronomically this year due to Covid-19. Consequently, numerous companies have been reliant on remote desktop connections to enable their employees to access their work computer from home.
One of the most popular applications for accessing Windows workstations and servers is Microsoft’s remote desktop protocol (RDP), which cyber criminals have viewed as the perfect opportunity to exploit.
To gain access to valuable corporate resources such as confidential emails and data, cyber criminals can deploy brute-force attacks, which attempt to find a valid RDP username and password pair by systematically checking all possible combinations until the right one is discovered.
Interested in the prevalence of RDP brute-force attacks, Reboot Online analyzed the latest data from anti-virus specialists Kaspersky to discover which Asian countries are most at risk.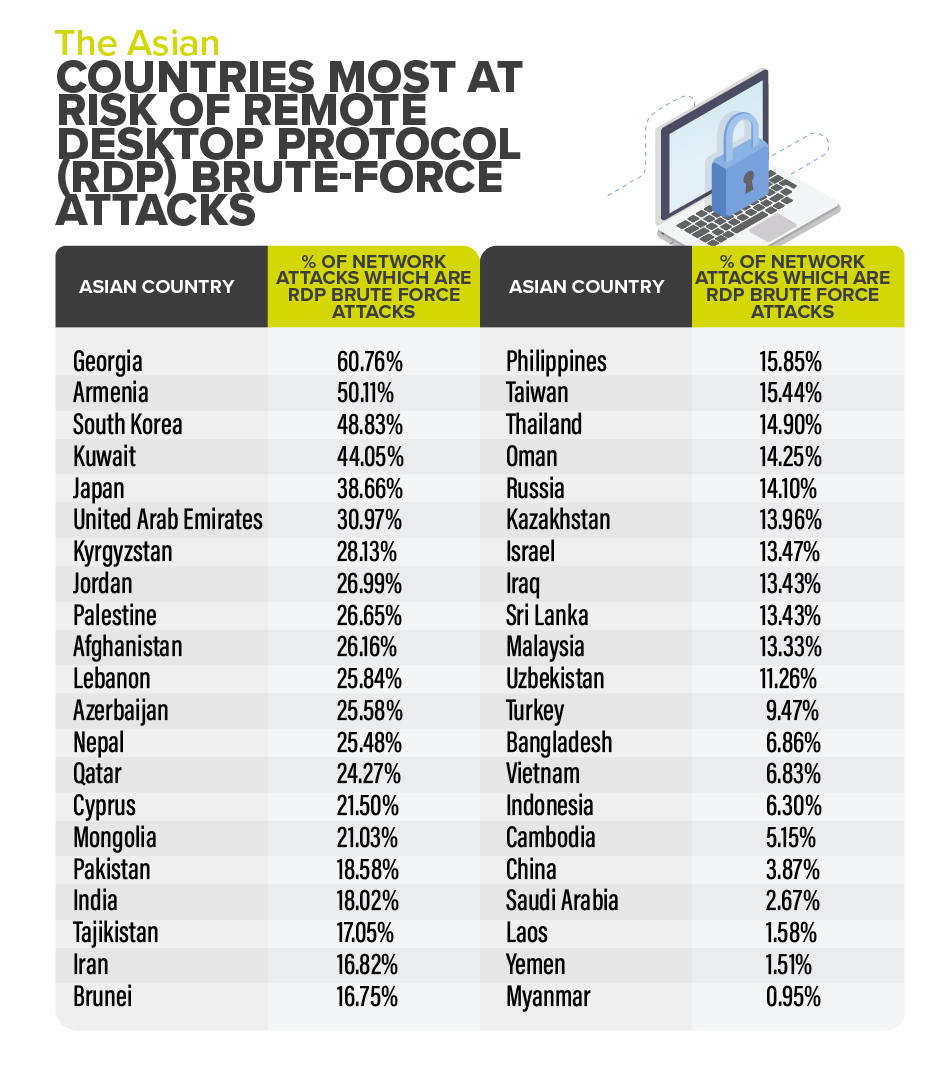 Reboot Online found that Georgia is the biggest victim of RDP brute-force attacks in Asia, with majority of network attacks attributed to RDP brute-force attacks (60.76%).
Reboot Online found that Georgia is the biggest victim of RDP brute-force attacks in Asia, with majority of network attacks attributed to RDP brute-force attacks (60.76%).
Armenia is in second position, as 50.11% of network attacks in the country are RDP brute-force attacks leaving Microsoft users at high risk.
Slightly below Armenia is South Korea, 48.83% of network attacks are RDP brute-force attacks, placing them as the third most likely to experience RDP brute-force attacks in Asia.
When it comes to the major economic powerhouses of Asia, this is how they fare with the risk of RDP brute-force attacks: Japan (38.66%), Pakistan (18.58%), India (18.02%), Russia (14.10%), Israel (13.47%), Turkey (9.47%), China (3.87%) and Saudi Arabia (2.67%).
Alternatively, Myanmar (0.95%), Yemen (1.51%) and Laos (1.58%) are among the Asian countries where RDP brute-force attacks are significantly lower, placing them at the bottom of the list.
In addition, Reboot Online provides advice on how to prevent RDP brute-force attacks:
- Have strong usernames and passwords: a basic and easy form of defense against RDP brute-force attacks is having a strong password. A password which is long and contains a combination of upper-and-lower case letters, numbers and special characters is recommended. Additionally, avoid basic account names such as ‘administrator’ as usernames, and instead use something more cryptic.
- Set remote access restrictions: instead of granting access to RDP to everyone in the company, think about the employees or departments who truly need it to work. By restricting RDP access to selected personnel, you take a productive step towards reducing the risk of an attack.
- Account lockout policy: RDP brute-force attacks could require cyber criminals hundreds, thousands or even millions of login attempts before finding the correct credentials –slow potential attacks by setting up an account lockout policy on Microsoft Windows. This feature will lock a user if they fail to log-in after a certain number of times within a specified time frame.
- Assess IT estate: Carefully assess all the computers in your company and identify any outdated units that can be accessed from the internet using RDP. Once these computers have been identified, replace them as soon as possible. Outdated computers are unlikely to support any new security updates/patches thus making them more susceptible to cyber-attacks. (Source: Reboot)
By MediaBUZZ


